NSO Group / Q Cyber Technologies
Over One Hundred New Abuse Cases
The May 2019 WhatsApp Incident
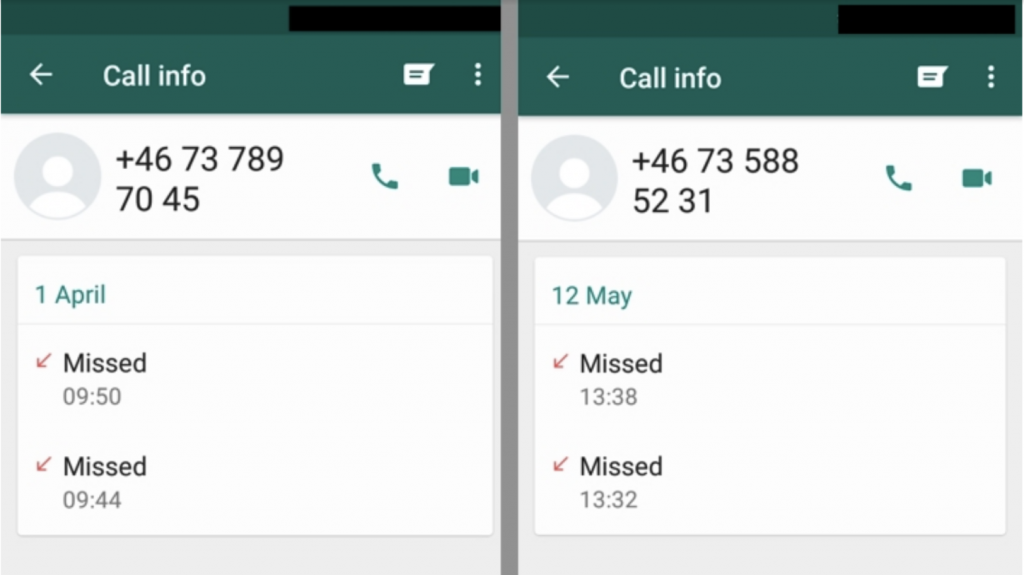
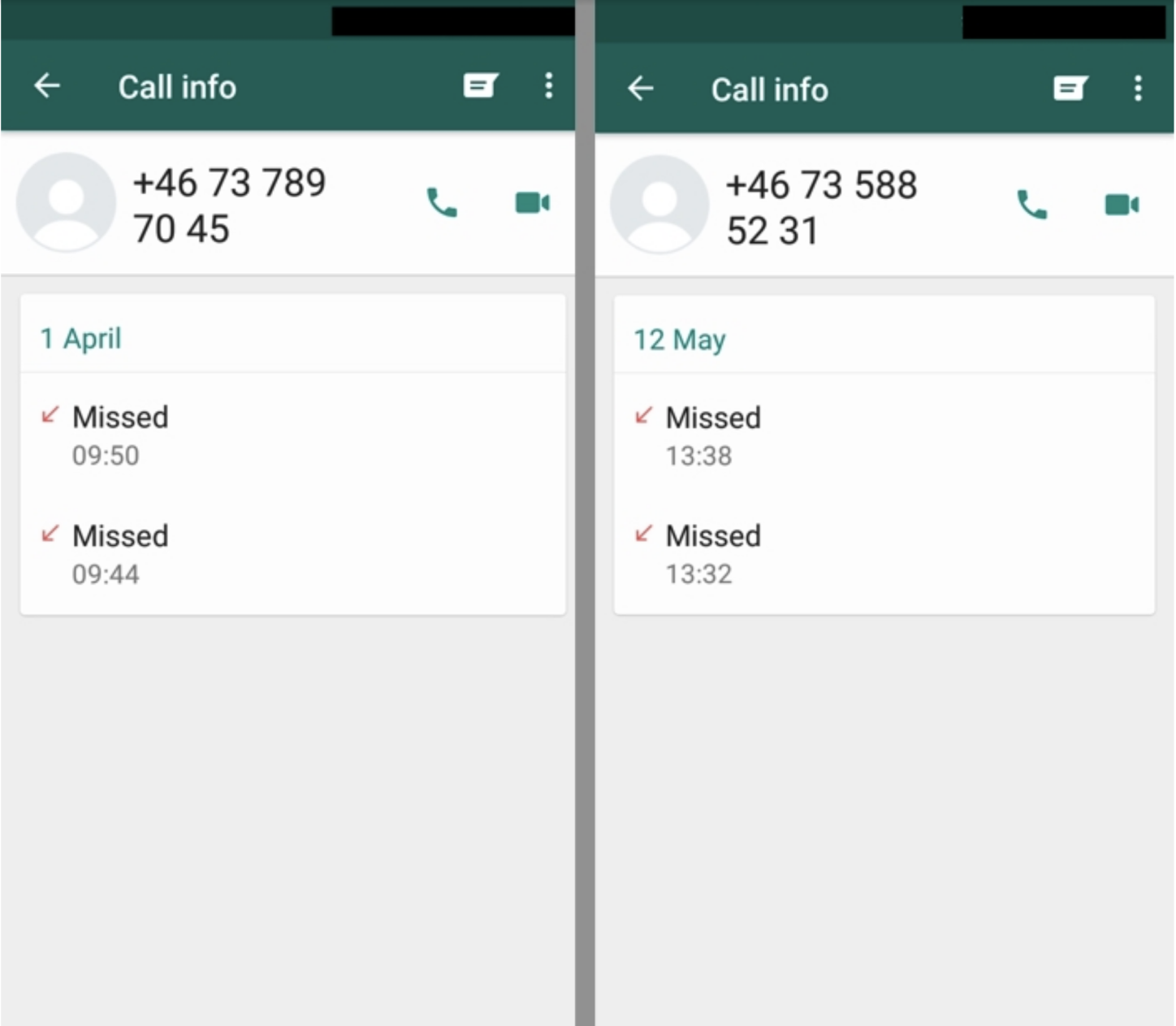
As reported in May 2019, WhatsApp identified and shortly thereafter fixed a vulnerability that allowed attackers to inject commercial spyware on to phones simply by ringing the number of a target’s device.
Today Oct 29th, WhatsApp is publicly attributing the attack to NSO Group, an Israeli spyware developer that also goes by the name Q Cyber Technologies.
Citizen Lab’s Role
After the incident, Citizen Lab volunteered to help WhatsApp identify cases where the suspected targets of this attack were members of civil society, such as human rights defenders and journalists.
We continue to investigate the incident, and conduct outreach with the individuals targeted with these attacks to assist them in becoming more secure, and to better understand the cases.
What is NSO?
NSO Group, which also goes by the name Q Cyber Technologies, is an Israeli-based company which develops and sells spyware technology. It is majority owned by Novalpina Capital, a European private equity firm. For more information on NSO Group, you can find a summary of key public reporting here.
NSO Group claims it sells its spyware strictly to government clients only, and all of its exports are undertaken in accordance with Israeli government export laws and oversight mechanisms. However, the number of cases in which their technology is used to target members of civil society continues to grow.
A Multi-Year History of Abuses
Citizen Lab—along with organizations such as R3D, Privacy International, EFF, and Amnesty International—has closely tracked how NSO Group’s surveillance technology has been turned against political dissidents, lawyers, journalists, and human rights defenders. Among the many companies Citizen Lab has tracked, NSO Group stands out in terms of the reckless abuse of its spyware by government clients. Although the technology is marketed as a tool to assist governments in lawful investigations into crime and terrorism, Citizen Lab has identified dozens of cases where journalists, human rights activists and defenders, lawyers, international investigators, political opposition groups, and other members of civil society have been targeted with its spyware, called “Pegasus.”
What is Pegasus?
NSO Group / Q Cyber Technologies’ flagship spyware, which is usually branded as Pegasus but which may have other names (including Q Suite), is among some of the most sophisticated spyware available on the market and can infiltrate both iOS and Android devices. To monitor a target, a Pegasus operator uses multiple vectors and tactics (see: ‘How Do Infections Happen?’), including zero-day exploits and deception, to penetrate security features in popular operating systems and silently install Pegasus without the user’s knowledge or permission.
What Can Pegasus Do?
Once Pegasus is installed, it begins contacting the operator’s command and control (C&C) servers to receive and execute operators’ commands, and send back the target’s private data, including passwords, contact lists, calendar events, text messages, and live voice calls from popular mobile messaging apps. The operator can even turn on the phone’s camera and microphone to capture activity in the phone’s vicinity, and use the GPS function to track a target’s location and movements.
How Do Infections Happen?
The spyware can be placed on phones using multiple vectors, or means of infection. The WhatsApp exploit from May 2019 was one such vector.
Other vectors used in prior cases of NSO targeting include tricking targets into clicking on a link using social engineering. For example, in 2017, the wife of a murdered Mexican journalist was sent alarming text messages concerning her husband’s murder, designed to trick her into clicking on a link and infecting her phone with the Pegasus spyware. In 2018, a close confidant of Jamal Khashoggi was targeted in Canada with a fake package notification, resulting in the infection of his iPhone. Citizen Lab has tracked more than two dozen cases using similar techniques.
Not all vectors are publicly known. Once the spyware is implanted, it provides a C&C server with regular, scheduled updates designed to avoid extensive bandwidth consumption. Pegasus is designed to be stealthy and evade forensic analysis, avoid detection by anti-virus software, and can be deactivated and removed by operators.
Commercial Spyware Abuse: A Global Problem
NSO Group has claimed that it has strict controls over how its spyware is sold and used, and robust company oversight mechanisms to prevent abuse. The new majority owner, Novalpina, has pledged to bolster these mechanisms in various ways. However, Citizen Lab research, and the research of other groups, has consistently presented a different and more troubling picture of abuse. Citizen Lab and others have repeatedly raised questions to Novalpina and NSO Group about whether their public statements about human rights compliance will make a difference in practice, pointing to inconsistencies and contradictions in their purported due diligence. NSO Group and Novalpina Capital have dismissed these questions and concerns.
The WhatsApp incident, and the more than 100 cases of abusive targeting that are associated with it, clearly verify the serious concerns Citizen Lab and others have raised. NSO Group spyware is being sold to government clients without appropriate controls over how it is employed by those clients. They are, in turn, using NSO’s technology to hack into the devices of members of civil society, including journalists, lawyers, political opposition, and human rights defenders—with potential lethal consequences.
We believe that remedying this problem will not be easy or simple. It will require a coalition of stakeholders, including governments, the private sector, and civil society to reign in what is now a “wild west” of unmitigated abuse. As it stands, NSO Group and other spyware companies are equipping repressive governments with powerful tools to spy on those who hold them to account. With powerful surveillance technology such as this roaming free, there is nowhere to hide and no one will be safe from those who wish to cause harm. Not acting urgently on this critical public emergency threatens liberal democracy and human rights worldwide.
More on Citizen Lab’s research and engagement on NSO Group can be found here.

