On December 15, 2022, as part of our regular re-analysis of past cases to find additional spyware infection indicators and details, we discovered that a researcher had misread the labels assigned to two individuals’ results, leading to a confusion between phones owned by two people with the same initials who were part of the same […]
“Smart” in-store shopping carts, developed by Caper and used by Sobeys, issue electronic receipts via SMS message and share a URL that uses an easily predictable format. These receipts contain a number of personal data points, including the customer’s partial credit/debit/Air Miles card numbers, a full list of purchases, and the date, time, and location of the customer’s purchase.
On May 7 2020, the Citizen Lab published a report that documents how WeChat (the most popular social app in China) conducts surveillance of images and files shared on the platform and uses the monitored content to train censorship algorithms. This document provides a summary of the research findings and questions and answers from the research team.
This document provides a high-level introduction to deep packet inspection, Internet filtering, and targeted intrusion dual-use technologies with the aim of familizaring the reader with their key technical features, the surrounding international human rights law framework, and some of the leading research to date on their deployment.
In the days leading up to the 30th anniversary of June 4 1989, YY, a popular live streaming platform in mainland China, updated its keyword blacklists with content focused on Democracy Movement related memorials and activism in Hong Kong.
This report demonstrates the technical underpinnings of how WeChat image censorship operates and suggests possible evasion strategies.
This report analyzes the information control practices related to a national crackdown on Chinese rights lawyers and activists on two leading Chinese social media networks. We document the Search filtering on Weibo, China’s Twitter-like service, as well as keyword and image censorship on WeChat, the most popular chat app in China.
A CBC article exploring the Chinese government’s use of surveillance techniques, what has been called the “Great Firewall,” highlights Citizen Lab’s work in studying the state and private enterprises that support it. In an interview, Citizen Lab Director Ron Deibert comments on the surveillance practices that the regime uses.
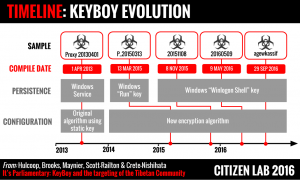
In this report we track a malware operation targeting members of the Tibetan Parliament that used known and patched exploits to deliver a custom backdoor known as KeyBoy. We analyze multiple versions of KeyBoy revealing a development cycle focused on avoiding basic antivirus detection.
A new report from the University of Toronto’s Citizen Lab identifies security and privacy issues in QQ Browser, a mobile browser produced by China-based Internet giant Tencent, which may put many millions of users of the application at risk of serious compromise.