Research
On May 7 2020, the Citizen Lab published a report that documents how WeChat (the most popular social app in China) conducts surveillance of images and files shared on the platform and uses the monitored content to train censorship algorithms. This document provides a summary of the research findings and questions and answers from the research team.
WeChat communications conducted entirely among non-China-registered accounts are subject to pervasive content surveillance that was previously thought to be exclusively reserved for China-registered accounts.
In this note, we describe a security issue where users in the “Waiting Room” of a Zoom meeting could have spied on the meeting, even if they were not approved to join. Zoom fixed the issue after we reported it to them.
This report examines the encryption that protects meetings in the popular Zoom teleconference app. We find that Zoom has “rolled their own” encryption scheme, which has significant weaknesses. In addition, we identify potential areas of concern in Zoom’s infrastructure, including observing the transmission of meeting encryption keys to China.
The analysis of YY and WeChat indicates broad censorship—blocking sensitive terms as well as general information and neutral references—potentially limiting the public’s ability to access information that may be essential to their health and safety.
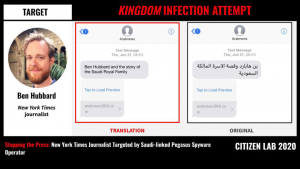
New York Times journalist Ben Hubbard was targeted with NSO Group’s Pegasus spyware via a June 2018 SMS message promising details about “Ben Hubbard and the story of the Saudi Royal Family.” The SMS contained a hyperlink to a website used by a Pegasus operator that we call KINGDOM. We have linked KINGDOM to Saudi Arabia. In 2018, KINGDOM also targeted Saudi dissidents including Omar Abdulaziz, Ghanem al-Masarir, and Yahya Assiri, as well as a staff member at Amnesty International.
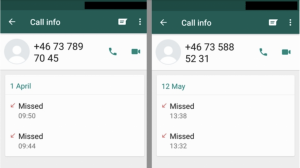
The May 2019 WhatsApp Incident As reported in May 2019, WhatsApp identified and shortly thereafter fixed a vulnerability that allowed attackers to inject commercial spyware on to phones simply by ringing the number of a target’s device. Today Oct 29th, WhatsApp is publicly attributing the attack to NSO Group, an Israeli spyware developer that also […]
Using the AMI approach, partners have launched projects around the world, including in Australia, Canada, Hong Kong, Indonesia, Malaysia, and South Korea. These projects focused on making data access requests to telecommunications companies in each country, led by a local researcher and a team of volunteers. Every country has specific laws, regulations, and corporate mechanisms that present unique challenges and opportunities in accessing data, but the results of each provide insights into the larger ecosystem of data access.
This report presents results from a series of research projects that measured responses to personal data requests from telecommunication companies and Internet Service Providers across jurisdictions in Asia including Australia, Hong Kong, South Korea, Indonesia, and Malaysia. Overall, the projects found responses from telecoms were incomplete and in some cases did not follow what is required by law.
This campaign is the first documented case of one-click mobile exploits used to target Tibetan groups, and reflects an escalation in the sophistication of digital espionage threats targeting the community.