Research
This project is a large-scale comparison of the three services, matching thousands of Chinese-language Wikipedia articles with their in-China counterparts, in order to identify the “content gaps” in the two baike. The difficulties of identifying traditional cases of information control in environments with distributed oversight like online enclopedias will be discussed. The research methodology and some of the initial results (including tables of possibly censored articles) will also be presented.
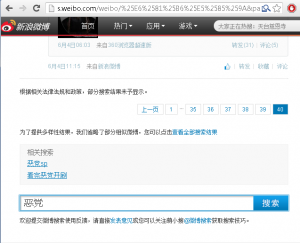
The China Chats keyword list was tested on Sina Weibo four times from Jun to Aug 2013. The data allows us to identify changes in censorship on Sina Weibo over time.
In this post, we report on “Surtr”, a malware family that has been used in targeted malware campaigns against the Tibetan community since November 2012
The Citizen Lab is pleased to announce the release of Some Devices Wander by Mistake: Planet Blue Coat Redux. In this report, we use a combination of network measurement and scanning methods and tools to identify instances of Blue Coat ProxySG and PacketShaper devices. This equipment can be used to secure and maintain networks, but can also be used to implement politically-motivated restrictions on access to information, and monitor and record private communications. We found Blue Coat devices on public networks of 83 countries. Included in these countries are regimes with questionable human rights records, and three countries that are subject to US sanctions: Iran, Syria, and Sudan.
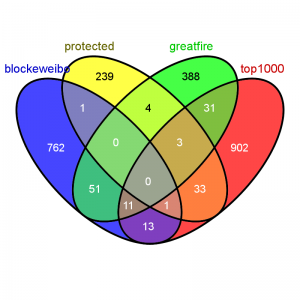
Working with the just-released China Chats keyword list, Jason Q. Ng extended The Citizen Lab/UNM’s analysis by checking whether each of the 4,256 keywords was blocked from searching on Sina Weibo. This report includes further analysis and examination of other potential censorship tactics by Weibo revealed in the data.
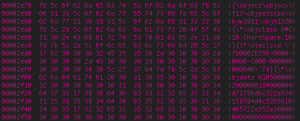
In this collaborative study between the Citizen Lab and Department of Computer Science at the University of New Mexico we examine the implementation of censorship and surveillance in two IM clients maintained by two different Chinese companies. For a period of more than a year and a half, we downloaded and decrypted the censorship and surveillance keyword lists used by the client software of two IM programs used in China: TOM-Skype and Sina UC.
The Citizen Lab is pleased to announce the publication of A Call to Harm: New Malware Attacks Against the Syrian Opposition. This research report by Morgan Marquis-Boire and John Scott-Railton examines two recent cyber attacks targeting the Syrian opposition: malware masquerading as the circumvention tool Freegate and a campaign masquerading as a call to arms by a pro-opposition cleric.
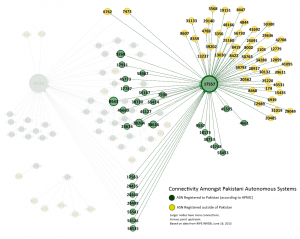
A new Citizen Lab report, entitled O Pakistan, We Stand on Guard for Thee: An Analysis of Canada-based Netsweeper’s Role in Pakistan’s Censorship Regime, has found that Canada-based Netsweeper filtering products have been installed in Pakistan, and are being used for filtering political and social web content.
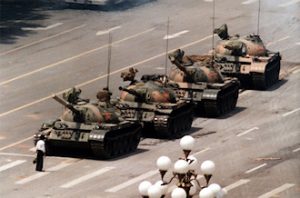
As citizens in China commemorate the twenty-fourth anniversary of June 4th today, we identified 71 keywords that are currently blocked from searching on Sina Weibo.
Citizen Lab is pleased to announce the release of “For Their Eyes Only: The Commercialization of Digital Spying.” The report features new findings, as well as consolidating a year of our research on the commercial market for offensive computer network intrusion capabilities developed by Western companies.