Research
Titled, “Internet Security and Networked Governance in International Relations”, the paper asks whether the Internet’s heavy reliance on nonhierarchical, networked forms of governance is compatible with growing concerns about cyber-security from traditional state actors.
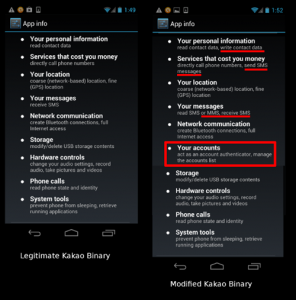
This blog post reports on a malware attack in which a compromised version of Kakao Talk, an Android-based mobile messaging client, was sent in a highly-targeted email to a prominent individual in the Tibetan community. The malware is designed to send a user’s contacts, SMS message history, and cellular network location to attackers. This post was updated on 18 April 2013.
Stefania Milan has co-authored an article with Arne Hintz, titled “Networked Collective Action and the Institutionalized Policy Debate: Bringing Cyberactivism to the Policy Arena?”,
Citizen Lab Fellow Stefania Milan has authored a chapter titled “WikiLeaks, Anonymous, and the Exercise of Individuality: Protesting in the Cloud” in the newly-released book, Beyond WikiLeaks: Implications for the Future of Communications, Journalism and Society.
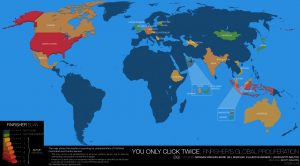
This post describes the results of a comprehensive global Internet scan for the command and control servers of FinFisher’s surveillance software. It also details the discovery of a campaign using FinFisher in Ethiopia that may have been used to target individuals linked to an opposition group. Additionally, it provides examination of a FinSpy Mobile sample found in the wild, which appears to have been used in Vietnam.
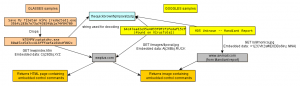
In this research brief, Seth Hardy describes malware (“GLASSES”) sent in 2010 that is a simple downloader closely related to malware described by Mandiant in their APT1 report. GLASSES appears to be a previous version of malware called GOGGLES by Mandiant, and was sent in a highly targeted email to a Tibetan human rights organization, demonstrating that APT1 is involved in more than just industrial and corporate espionage.
Titled “800 Titles but no policy – Thoughts on Cyber Warfare,” the piece examines the cyber arms race and government responses to cyber warfare threats.
Blue Coat Devices capable of filtering, censorship, and surveillance are being used around the world. 61 of these Blue Coat appliances are on public or government networks in countries with a history of concerns over human rights, surveillance, and censorship. Our findings support the need for national and international scrutiny of Blue Coat implementations in the countries we have identified, and a closer look at the global proliferation of “dual-use” information and communication technologies.
This appendix contains countries of interest in which Blue Coat devices were located.
A joint investigation by Agentura.Ru, CitizenLab and Privacy International was published in Wired Magazine on 21 December, 2012.