Research
The Citizen Lab and Access Now have confirmed 35 cases of journalists and members of civil society whose phones were successfully infected with NSO’s Pegasus spyware between July 2020 and November 2021. We shared a sample of forensic data with Amnesty International’s Security Lab which independently confirms the findings.
Two Egyptians—exiled politician Ayman Nour and the host of a popular news program (who wishes to remain anonymous)—were hacked with Predator spyware, built and sold by the previously little-known mercenary spyware developer Cytrox. The phone of Ayman Nour was simultaneously infected with both Cytrox’s Predator and NSO Group’s Pegasus spyware, operated by two different government clients.
Front Line Defenders’ analysis indicated that six devices belonging to six Palestinian human rights defenders were hacked with Pegasus, a spyware developed by the cyber-surveillance company NSO Group. Both the Citizen Lab and Amnesty International’s Security Lab independently confirmed these findings.
China’s sophisticated filtering system, known as the Great Firewall (GFW), is the region’s biggest impediment to the freedom of information. The GFW is built by the Chinese government and is continuously developed to serve their political interests. In this report, we introduce the design of GFWatch, a large-scale longitudinal measurement platform that informs the public about how GFW censorship changes over time and its negative impact on the free flow of information.
Our forensic analysis of two iPhones belonging to Hubbard found evidence of Pegasus infections in July 2020 and June 2021. Notably, these infections occurred after Hubbard reported in January 2020 that we found that he was targeted in 2018 by the Saudi Arabia-linked Pegasus operator that we call KINGDOM.
“Smart” in-store shopping carts, developed by Caper and used by Sobeys, issue electronic receipts via SMS message and share a URL that uses an easily predictable format. These receipts contain a number of personal data points, including the customer’s partial credit/debit/Air Miles card numbers, a full list of purchases, and the date, time, and location of the customer’s purchase.
Citizen Lab researchers reviewed the consultation materials, including the “Technical Paper” and the “Discussion Guide” associated with the government’s proposal to address what it has referred to as “online harms.” We provide the following comments in response to that consultation process.
On September 28, the Citizen Lab published an analysis of COVID-19 data collection practices. In this post, we discuss the significance of the findings with report authors.
In this report, we undertake a preliminary comparative analysis of how different information technologies were mobilized in response to COVID-19 to collect data, the extent to which Canadian laws impeded the response to COVID-19, and the potential consequences of reforming data protection or privacy laws to enable more expansive data collection, use, or disclosure of personal information in future health emergencies.
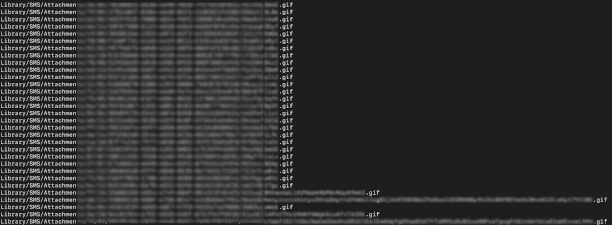
While analyzing the phone of a Saudi activist infected with NSO Group’s Pegasus spyware, we discovered a zero-day zero-click exploit against iMessage. The exploit, which we call FORCEDENTRY, targets Apple’s image rendering library, and was effective against Apple iOS, MacOS and WatchOS devices.