Publications
This report describes the results of two independent security audits of Smart Sheriff, one by researchers who collaborated at the 2015 Citizen Lab Summer Institute (held at the Munk School of Global Affairs, University of Toronto), and the other by the auditing firm Cure53. The combined audits identified twenty-six security vulnerabilities in recent versions of Smart Sheriff (versions 1.7.5 and under). These vulnerabilities could be leveraged by a malicious actor to take control of nearly all Smart Sheriff accounts and disrupt service operations.
This report describes an elaborate phishing campaign using two-factor authentication against targets in Iran’s diaspora, and at least one Western activist.
This post analyzes targeted malware attacks against groups in the Tibetan diaspora and Hong Kong that leverage the CVE-2014-4114 vulnerability
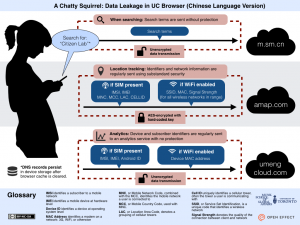
UC Browser is the most popular mobile web browser in China and India, boasting over 500 million users. This report provides a detailed analysis of how UC Browser manages and transmits user data, particularly private data, during its operation. Our research was prompted by revelations in a document leaked by Edward Snowden on which the Canadian Broadcasting Corporation (CBC) was preparing a story.
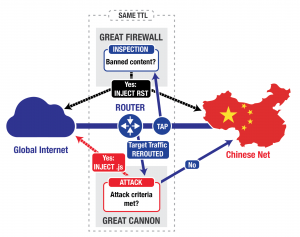
This post describes our analysis of China’s “Great Cannon,” our term for an attack tool that we identify as separate from, but co-located with, the Great Firewall of China. The first known usage of the Great Cannon is in the recent large-scale novel DDoS attack on both GitHub and servers used by GreatFire.org.