Publications
Hundreds of members of the Tibetan community are being targeted by email-based malware attacks that leverage the March 10 Tibetan Uprising anniversary as a theme. This report analyzes two March 10 related attacks. One using a new malware family we call MsAttacker , and another using the ShadowNet malware family and command and control infrastructure related to previous campaigns that targeted the Tibetan community.
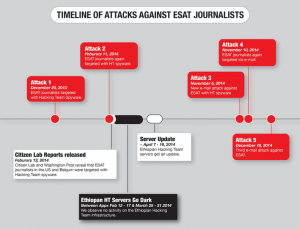
The research findings documented in this report suggest that Hacking Team may have continued to provide updated versions of its spyware to the same attacker who have targeted ESAT journalists based in the United States in 2014, despite reports of use of the spyware against journalists.
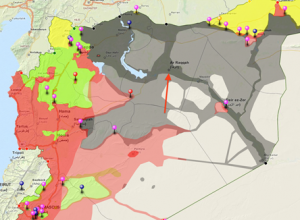
Citizen Lab Research Fellow John Scott-Railton is one of the authors of a report entitled “Behind the Syrian Conflict’s Digital Frontlines,” released today by FireEye, that documents a hacking operation that successfully breached the Syrian opposition.
This report describes a malware attack on a Syrian citizen media group critical of Islamic State of Iraq and Syria (ISIS). Though we are unable to conclusively attribute the attack to ISIS or its supporters, a link to ISIS is plausible. The malware used in the attack differs substantially from campaigns linked to the Syrian regime, and the attack is against a group that is an active target of ISIS forces. In the interest of highlighting a developing threat, this post analyzes the attack and provides a list of Indicators of Compromise.
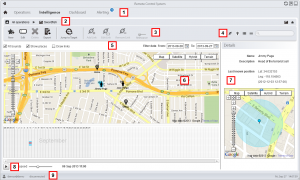
We analyze a newly discovered Android implant that we attribute to Hacking Team and highlight the political subtext of the bait content and attack context. In addition, we expose the functionality and architecture of Hacking Team’s Remote Control system and operator tradecraft in never-before published detail.