Bad Connection
FAQ
Research FAQ for the report “Bad Connection: Uncovering Global Telecom Exploitation by Covert Surveillance Actors”
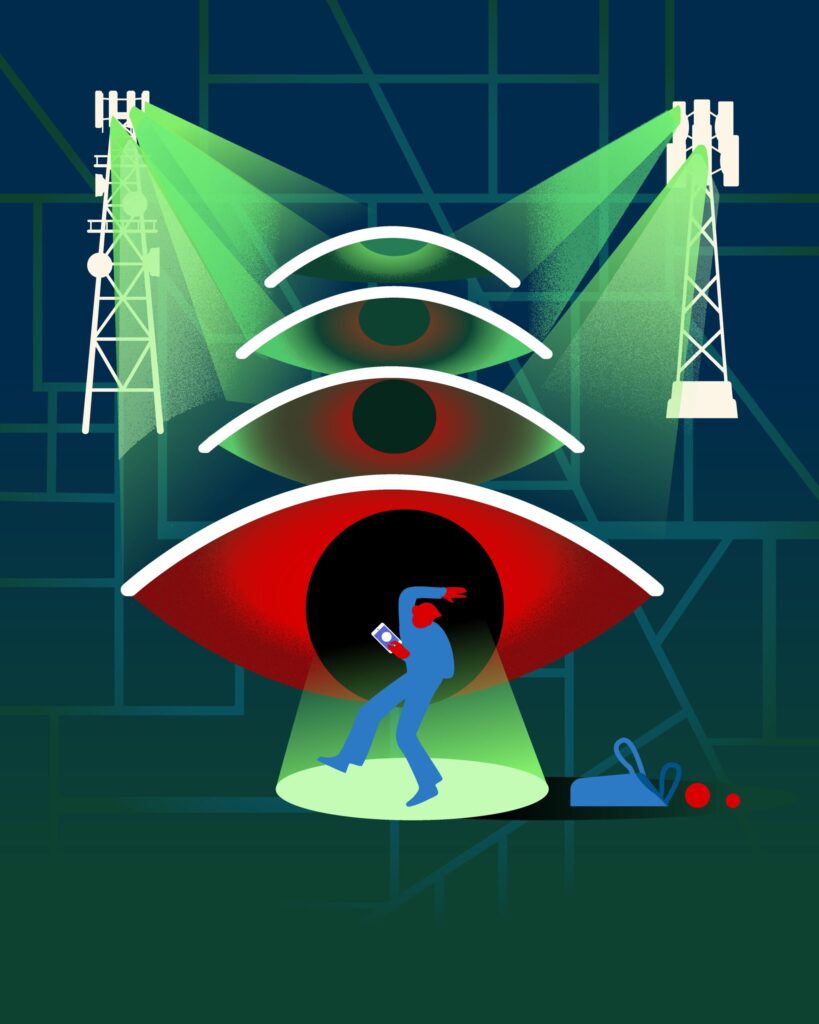
The mobile networks that our phones connect to and rely on contain inherent vulnerabilities that can be exploited to track users and access sensitive information. As state-sponsored cyber-espionage groups and commercial surveillance have expanded, these risks have grown in both scale and sophistication. In our 2023 report, Finding You, we demonstrated how these vulnerabilities are used to track individuals. In Bad Connection, we identify two sophisticated surveillance campaigns, link them to real-world attack traffic, and for the first time, to mobile operator signaling infrastructure.
Why is this important?
This investigation shows how weaknesses in technology and governance allow mobile networks to be used as covert surveillance platforms. For the first time, we demonstrate how surveillance actors gain access to the global telecom interconnect ecosystem and use it to carry out tracking operations. By leasing or obtaining access to legitimate network entry points, they can hide surveillance traffic and operate as trusted operators.
What makes telecommunications protocols so vulnerable?
The mobile ecosystem includes over a thousand operators worldwide that interconnect through signaling protocols and roaming agreements, allowing phones to function seamlessly across countries. These protocols were originally designed for a smaller, trusted community of operators and lack strong security protections. Our report shows how this trusted infrastructure is now being leveraged to support covert surveillance.
Unlike conventional cyber espionage campaigns, telecommunication-level surveillance is almost entirely invisible. Risks also arise because 3G, 4G, and 5G protocols are used alongside each other. While 4G and 5G are more secure, roaming devices often register to both 3G and 4G simultaneously, creating additional avenues of attack.
What is the difference between 3G, 4G, and 5G?
3G networks use the older SS7 signaling protocol, while 4G and most 5G networks use the Diameter protocol for inter-operator signaling. While Diameter should be more secure, the industry has failed to implement the latest security features, where significant vulnerabilities remain.
How do attackers gain access?
Attackers generally take the path of least resistance to gain access to the mobile network ecosystem. Many telecom providers maintain connections to international signaling networks to support services like roaming or delivering international SMS messages. By purchasing access through legitimate operators or third-party providers, actors can obtain indirect access to this system. From here, they can send tracking requests that appear to come from legitimate operators, allowing them to mask their identity while attempting to discover the location of their target.
Another method sends a specially formatted SMS message to the target’s SIM card. These messages are invisible to the user and can trigger the phone to collect and transmit location data, effectively turning the device into a tracking beacon.
Who are the perpetrators?
We found evidence pointing to platforms leveraging operator networks based in Israel, the U.K., and the Channel Islands. These same countries have been linked in prior public investigations to coordinated, commercial espionage organizations targeting mobile users.
It’s important to note that this does not necessarily imply that the operator networks were involved in attacks. In some cases, access to the signaling ecosystem can be obtained through third party providers, commercial leasing arrangements, or other intermediary services that allow actors to send messages using signaling identifiers from legitimate networks.
While at this time we do not attribute this campaign to a specific actor, the evidence is consistent with a commercially developed telecom surveillance platform supporting government intelligence activities.
Who does this affect? Is my communication safe?
These attacks are entirely invisible to users, so it isn’t possible to know if someone in particular is being targeted. Typically, these surveillance campaigns target high-profile individuals and are not used for mass surveillance. So far, we have not identified any instances of regular users being tracked.

