spyware
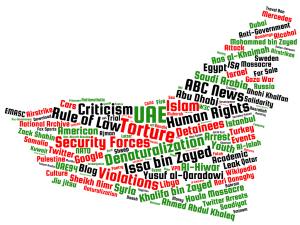
This report describes a campaign of targeted spyware attacks carried out by a sophisticated operator, which we call Stealth Falcon. The attacks have been conducted from 2012 until the present, against Emirati journalists, activists, and dissidents.
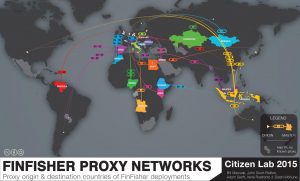
This post describes the results of Internet scanning we conducted to identify the users of FinFisher, a sophisticated and user-friendly spyware suite sold exclusively to governments.
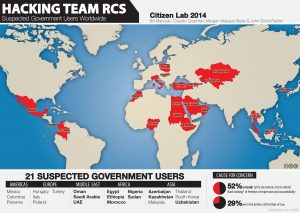
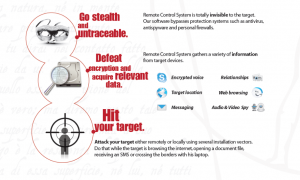
This report outlines an extensive US nexus for a network of servers forming part of the collection infrastructure of Hacking Team’s Remote Control System. The network, which includes data centers across the US, is used to obscure government clients of Hacking Team. It is used by at least 10 countries ranging from Azerbaijan and Uzbekistan to Korea, Poland and Ethiopia. In addition we highlight an intriguing US-only Hacking Team circuit.
This post is the second in a series of posts that focus on the global proliferation and use of Hacking Team’s RCS spyware, which is sold exclusively to governments.
In this report, we identified three instances where Ethiopian journalist group ESAT was targeted with spyware in the space of two hours by a single attacker. In each case the spyware appeared to be RCS (Remote Control System), programmed and sold exclusively to governments by Milan-based Hacking Team.
Citizen Lab is pleased to announce the release of “For Their Eyes Only: The Commercialization of Digital Spying.” The report features new findings, as well as consolidating a year of our research on the commercial market for offensive computer network intrusion capabilities developed by Western companies.
The use of remote surveillance software against activists has been a feature of the ongoing conflict in Syria. Today, the EFF and Citizen Lab report on the use of a new toolkit by a previously observed attacker. This actor has been circulating malware which surreptitiously installs BlackShades RAT on victims machines.