Research
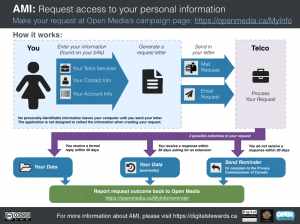
This post provides a summary of early findings associated with Canadians creating right to information requests using the Access My Info tool. It discusses several themes emergent from an analysis of company responses to such requests.
At USENIX Security 2014 Citizen Lab researchers presented two papers on targeted threats against civil society communities as part of a dedicated session on the topic entitled Tracking Targeted Attacks against Civilians and NGOs.
This report provides a detailed analysis of two products sold for facilitating targeted surveillance known as network injection appliances. These products allow for the easy deployment of targeted surveillance implants and are being sold by commercial vendors to countries around the world. Compromising a target becomes as simple as waiting for the user to view unencrypted content on the Internet.
In this report, we update the results of our June 2014 network measurement tests in Iraq in reaction to the ongoing insurgency in the country, and analyze two mobile applications, FireChat and Dawn of Glad Tidings.
In this post we report updates on how LINE, KakaoTalk, OneDrive and Flickr are being disrupted in China. We find that Flickr and OneDrive remain consistently blocked, but LINE and KakaoTalk show inconsistent fluctuation between accessibility and inaccessibility. We also analyze security and privacy of FireChat and test accessibility of the service in China.
In this post we examine how the Great Firewall of China is implementing DNS tampering and HTTP request filtering on KakaoTalk and LINE domains, which is disrupting service of the applications as a result. We find that Flickr and OneDrive are also blocked through DNS tampering. We also analyze recent changes to the LINE keyword filtering list.
This edition of Social Media Watch deals with top court rulings on digital privacy, social media monitoring, and mobile security news.
We analyze a newly discovered Android implant that we attribute to Hacking Team and highlight the political subtext of the bait content and attack context. In addition, we expose the functionality and architecture of Hacking Team’s Remote Control system and operator tradecraft in never-before published detail.
In this report, we document the results of network measurement tests we ran to determine how the Internet is being filtered in Iraq in reaction to ongoing insurgency in the country. The results identify 20 unique URLs that are blocked on three Iraq-based Internet Service Providers. Notably, none of the 7 websites we tested that are affiliated with, or supportive, of the jihadist insurgent group the Islamic State in Iraq and Greater Syria (ISIS) were found to be blocked.
This post first identifies the individual and collective benefits of using the Access My Info tool to request access to one’s personal data held by Canadian data operators. It then discusses technical design decisions that went into the tool’s development and implementation.