Brief
Amnesty International’s Security Lab has just published Caught in the Net as part of the European Investigative Collaborations‘ Predator Files, which details a threat actor sending what they assess to be Predator infection links on social media in replies to Twitter / X posts by officials, journalists and other members of civil society. The Citizen […]
We identified widespread Pegasus spyware infections within Armenian civil society. We also identified two suspected Pegasus operators in Azerbaijan, whom we call BOZBASH and YANAR.
We confirm that in 2020 and 2021 we observed and notified the government of the United Kingdom of multiple suspected instances of Pegasus spyware infections within official UK networks, including the Prime Minister’s Office and the Foreign and Commonwealth Office.
Our forensic analysis confirms that phones belonging to three individuals in Bahrain were hacked in 2021 with NSO Group’s Pegasus spyware.
Front Line Defenders’ analysis indicated that six devices belonging to six Palestinian human rights defenders were hacked with Pegasus, a spyware developed by the cyber-surveillance company NSO Group. Both the Citizen Lab and Amnesty International’s Security Lab independently confirmed these findings.
“Smart” in-store shopping carts, developed by Caper and used by Sobeys, issue electronic receipts via SMS message and share a URL that uses an easily predictable format. These receipts contain a number of personal data points, including the customer’s partial credit/debit/Air Miles card numbers, a full list of purchases, and the date, time, and location of the customer’s purchase.
Forbidden Stories and Amnesty International requested that the Citizen Lab undertake an independent peer review of a sample of their forensic evidence and their general forensic methodology. We were provided with iTunes backups of several devices and a separate methodology brief, and independently validated that Amnesty International’s forensic methodology correctly identified infections with NSO’s Pegasus spyware.
For human rights activists, Internet technologies bring both risks and benefits. Smartphones are widely used to document the abuses that activists are fighting against, as well as to store photos, recordings, and documents. Social media and messaging apps are key organising and communications tools. But even as these technologies enhance activists’ work, they also enable online threats such as surveillance and harassment.
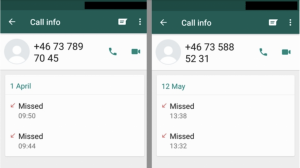
The May 2019 WhatsApp Incident As reported in May 2019, WhatsApp identified and shortly thereafter fixed a vulnerability that allowed attackers to inject commercial spyware on to phones simply by ringing the number of a target’s device. Today Oct 29th, WhatsApp is publicly attributing the attack to NSO Group, an Israeli spyware developer that also […]
Using the AMI approach, partners have launched projects around the world, including in Australia, Canada, Hong Kong, Indonesia, Malaysia, and South Korea. These projects focused on making data access requests to telecommunications companies in each country, led by a local researcher and a team of volunteers. Every country has specific laws, regulations, and corporate mechanisms that present unique challenges and opportunities in accessing data, but the results of each provide insights into the larger ecosystem of data access.