Publications
In this research note, we analyze a malware campaign targeting Hong Kong democracy activists. Two new malware families are used in the campaign that we name UP007 and SLServer. Previous reports have shown overlap in the tactics, tools, and procedures used in this campaign in other operations targeting groups in Burma, Hong Kong, and the Tibetan community.
This report describes the latest iteration in a long-running espionage campaign against the Tibetan community. We describe how the attackers continuously adapt their campaigns to their targets, shifting tactics from document-based malware to conventional phishing
A second audit of South Korea’s Smart Sheriff application reveals that there are numerous unresolved vulnerabilities that put minor children and parental users of the application at serious risk.
This report provides a detailed, mixed methods analysis of Information controls related to the Yemen armed conflict, with research commencing at the end of 2014 and continuing through October 20, 2015. The research confirms that Internet filtering products sold by the Canadian company Netsweeper have been installed on and are presently in operation in the state-owned and operated ISP YemenNet, the most utilized ISP in the country.
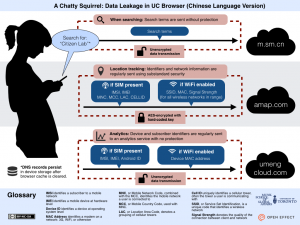
UC Browser is the most popular mobile web browser in China and India, boasting over 500 million users. This report provides a detailed analysis of how UC Browser manages and transmits user data, particularly private data, during its operation. Our research was prompted by revelations in a document leaked by Edward Snowden on which the Canadian Broadcasting Corporation (CBC) was preparing a story.