Hacking Team leak highlights Citizen Lab research
Media coverage: Fast Company, NPR, VICE Motherboard, CSO Online, Washington Post, The Intercept, Threatpost, The Korea Times, The Associated Press, The Hamilton Spectator, The Toronto Star.
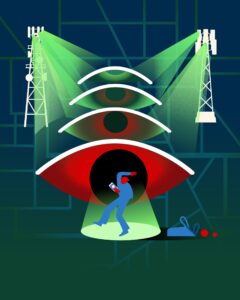
Hacking Team, a Milan-based developer of “offensive security” technology that markets its products to governments and law enforcement agencies around the world, was significantly compromised when hackers leaked nearly 400 GB of its internal data, including emails, client files, and financial documents. The leak was announced via Hacking Team’s own compromised Twitter account, and the content made publicly available. Among other things, the leaked documents confirmed our findings that the company sells its software to several governments with repressive human rights records, such as Ethiopia, Sudan, Saudi Arabia, Kazakhstan, and more.
Previous Citizen Lab Work
In 2012, the Citizen Lab started researching Hacking Team as a component of several overlapping interests, including technical research and documentation of targeted digital attacks on NGOs and human rights activists, and investigation of the global dissemination of commercial surveillance, filtering, and spyware products. Our first report on Hacking Team, “Backdoors are Forever: Hacking Team and the Targeting of Dissent?,” was published in 2012, when we discovered that a Moroccan civil society group’s computers and those of a prominent United Arab Emirates (UAE) human rights activist were compromised. We were able to positively identify the malicious software on those computers as a Hacking Team product sold to the Moroccan and UAE government secret services, respectively.
In 2014 we continued to publish reports on Hacking Team. The first report, “Hacking Team and the Targeting of Ethiopian Journalists,” showed that Ethiopia’s intelligence services were using Hacking Team’s products to hack and monitor Ethiopian-American journalists based in the United States and Belgium. That report led to front page coverage [PDF] in the Washington Post, and triggered extensive reporting on Hacking Team’s practices. Then, using network measurement techniques, we were able to positively identify the end-points and thus government clients of Hacking Team’s infrastructure in 21 countries, which we reported in “Mapping Hacking Team’s “Untraceable” Spyware”, including many that are notorious abusers of human rights. The final report, “Hacking Team’s US Nexus,” pointed out that Hacking Team products made extensive use of US-based servers to covertly exfiltrate hacked data, and pointed out the policy implications of hacked data transiting the United States. We followed up these reports with an open letter to Hacking Team asking for clarification about their due diligence in light of our findings. We did not receive a response.
Later in 2014, we followed up with two more reports. A report published in June, entitled “Police Story: Hacking Team’s Government Surveillance Malware,” highlighted that Hacking Team’s software appeared to be utilized against Shia minorities in Saudi Arabia through a backdoored copy of a legitimate Android news app, while a report published in August, “Schrodinger’s Cat Video and the Death of Clear-Text,” demonstrated how particular Hacking Team techniques could be used to remotely infect computers. Citizen Lab researchers Bill Marczak, Morgan Marquis-Boire, and John Scott-Railton, along with Professor Vern Paxson of Berkeley, also collaborated on a peer-reviewed academic publication, “When Governments Hack Opponents: A Look at Actors and Technology” [PDF], that laid out what we then knew about commercial malware, including a discussion of Hacking Team.
In 2015, despite the scrutiny and attention to potential abuses stemming from our reporting on the targeting of Ethiopian journalists, we uncovered strong evidence that the Ethiopian government was still receiving support from Hacking Team, as we reported in “Hacking Team Reloaded? US-Based Ethiopian Journalists Again Targeted with Spyware.” Furthermore, after a pause immediately following our 2014 report, attackers were again found to be targeting US-based journalists with Hacking Team spyware. We then wrote a second open letter to Hacking Team, requesting clarification about their customer policies and due diligence. We again did not receive a response.
The Leaks
The leaked emails validate key elements of our research. All of the countries we identified in previous research have been confirmed as Hacking Team clients, as are several other countries of major concern from a human rights perspective. Although Hacking Team publicly questioned the validity of our research, the company’s internal emails detail cases where Hacking Team engineers at times confirm our research. They show the company aggressively courting authoritarian and repressive regimes. In the case of Ethiopia, Hacking Team was aware that their product was used against journalists, yet continued to provide services to the client. Other leaked emails suggest the company attempted to obfuscate the truth to mislead journalists.
Citizen Lab Research Fellow Bill Marczak, who contributed to a series of Citizen Lab reports on Hacking Team, told the Washington Post that the company’s leaked internal reactions in the wake of these reports show that “their primary concern seems to have been not getting caught again.” Research Fellow Claudio Guarnieri, who also worked on Hacking Team reports by the Citizen Lab, told Threatpost that the company is just one of many that markets similar surveillance products. “Hacking Team is just one player in a big market. I suspect others will continue just fine, and probably Hacking Team itself will resurface in a while,” said Guarnieri. In an interview, Director Ron Deibert told the Toronto Star that it was interesting to see that Citizen Lab’s reports had an impact on Hacking Team, though he said that the leaked files were “very discouraging.” “Hacking Team is a symptom of a larger disease,” he added, referring to the sale of spyware to repressive regimes worldwide.
Read more of the Citizen Lab’s reports and posts relating to Hacking Team spyware.