FAQ
An Analysis of Indonesia and the Philippines’ Government-launched COVID-19 Apps
FAQ
On December 21, 2020 the Citizen Lab released a report that discovered issues with three COVID-related applications in Indonesia and the Philippines. This document provides a summary of the research findings and questions and answers from the research team.
- Why were PeduliLindungi, StaySafe PH, and COVID-KAYA chosen to be studied?
- What methods did researchers undertake to analyze these apps?
- What is the PeduliLindungi app used for? And what issues did you discover?
- What is the StaySafe PH app used for? And what issues did you discover?
- How did StaySafe’s developers address the security vulnerability?
- What is the COVID-KAYA app used for? And what issues did you discover?
- How do the findings of COVID-KAYA relate to the issues previously reported?
- What is the difference between a permission and a dangerous permission?
- What is the difference between dangerous permissions and vulnerabilities?
- What are unused permissions?
- What can app developers do to better protect the users of public health apps?
Why were PeduliLindungi, StaySafe PH, and COVID-KAYA chosen to be studied?
In July 2020, the Citizen Lab wrote a short blog post regarding COVID-19’s impact on marginalised communities in Indonesia, the Philippines, Singapore, and South Korea. Following this publication, we conducted an analysis of COVID-19 apps launched by the governments of Indonesia and the Philippines because of reported concerns over the collection of personal data through the apps (see Detik.com and INQUIRER.net for Indonesia’s and the Philippines’ apps respectively), as well as previous incidents of COVID-19-related data breaches in Indonesia and the Philippines.
What methods did researchers undertake to analyze these apps?
We decided to analyze the Android versions of the apps, as Android is the predominant mobile operating system used in the Southeast Asian region. We identified which dangerous permissions each app used, and, to understand why these apps requested each dangerous permission, we used a variety of methods including surveying media reports and previous analyses of the apps, as well as by reverse engineering each apps’ code and capturing their network traffic.
What is the PeduliLindungi app used for? And what issues did you discover?
PeduliLindungi began as Indonesia’s government-launched digital contact tracing application. Other features have been added to the app since it was launched at the end of March 2020. For example, a “digital diary” function that records a list of locations visited by the user when they scan government-provided QR codes, and a facial recognition function to measure the user’s temperature and to determine whether a mask or face covering is on before the user enters a public space or building.
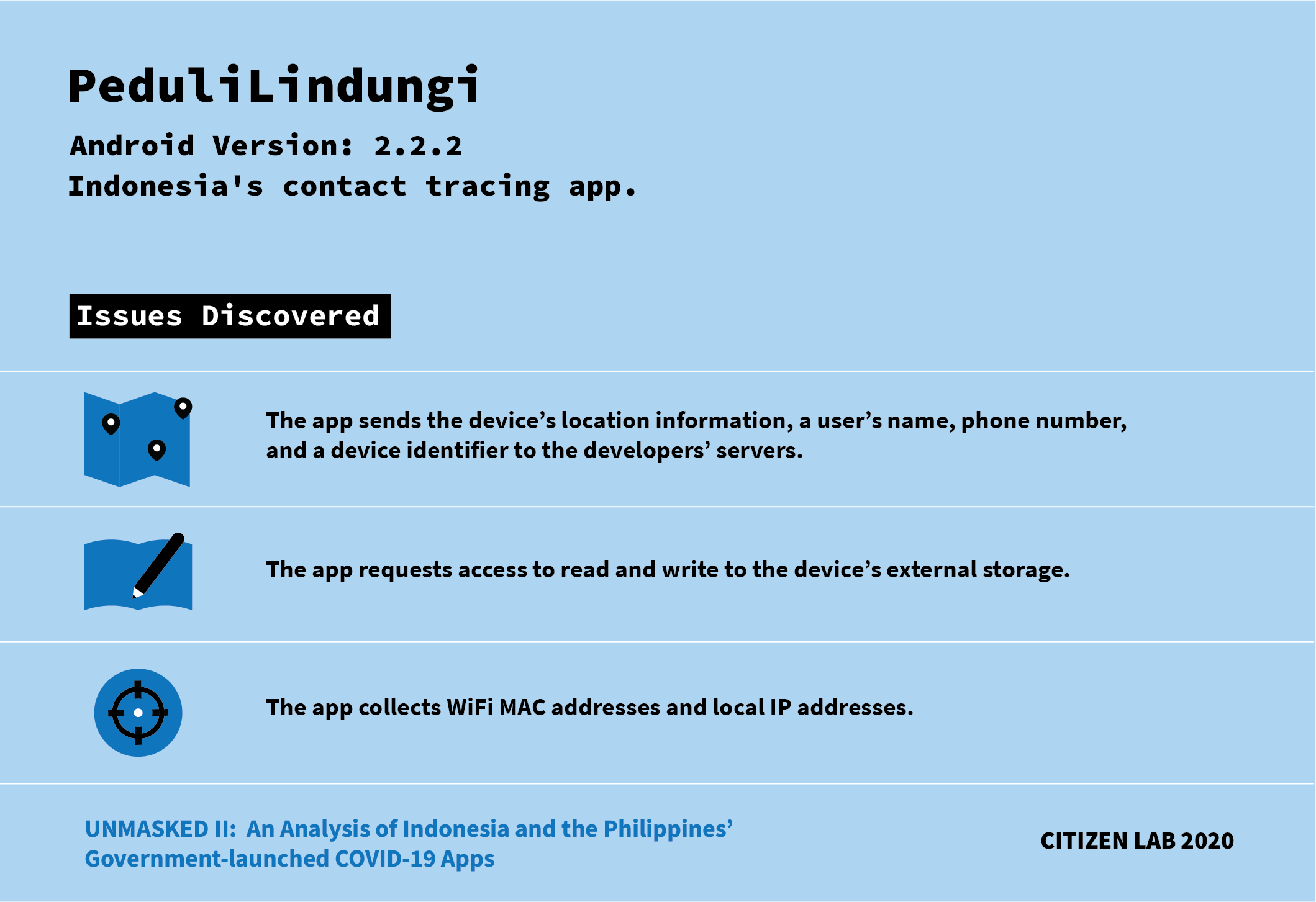
We discovered the following issues with the PeduliLindungi app:
- The app sends the device’s location information along with a user’s name, phone number, and a device identifier to the developers’ servers. This allows the developers to track the physical location of each individual device, which is not necessary for contact tracing.
- The app requests access to read and write to the device’s external storage. We found that this access is unnecessary to the app’s functionality.
- The app collects WIFI MAC addresses and local IP addresses. Both of these addresses can help identify a device or user and are unnecessary for contact tracing.
- When inspecting PeduliLindungi’s source code, we found that it contains a “root” detection library. Root detection is a common method developers use to make reverse engineering more difficult.
What is the StaySafe PH app used for? And what issues did you discover?
StaySafe PH is the Philippines’ officially adopted contact tracing and COVID-19 symptom monitoring app.
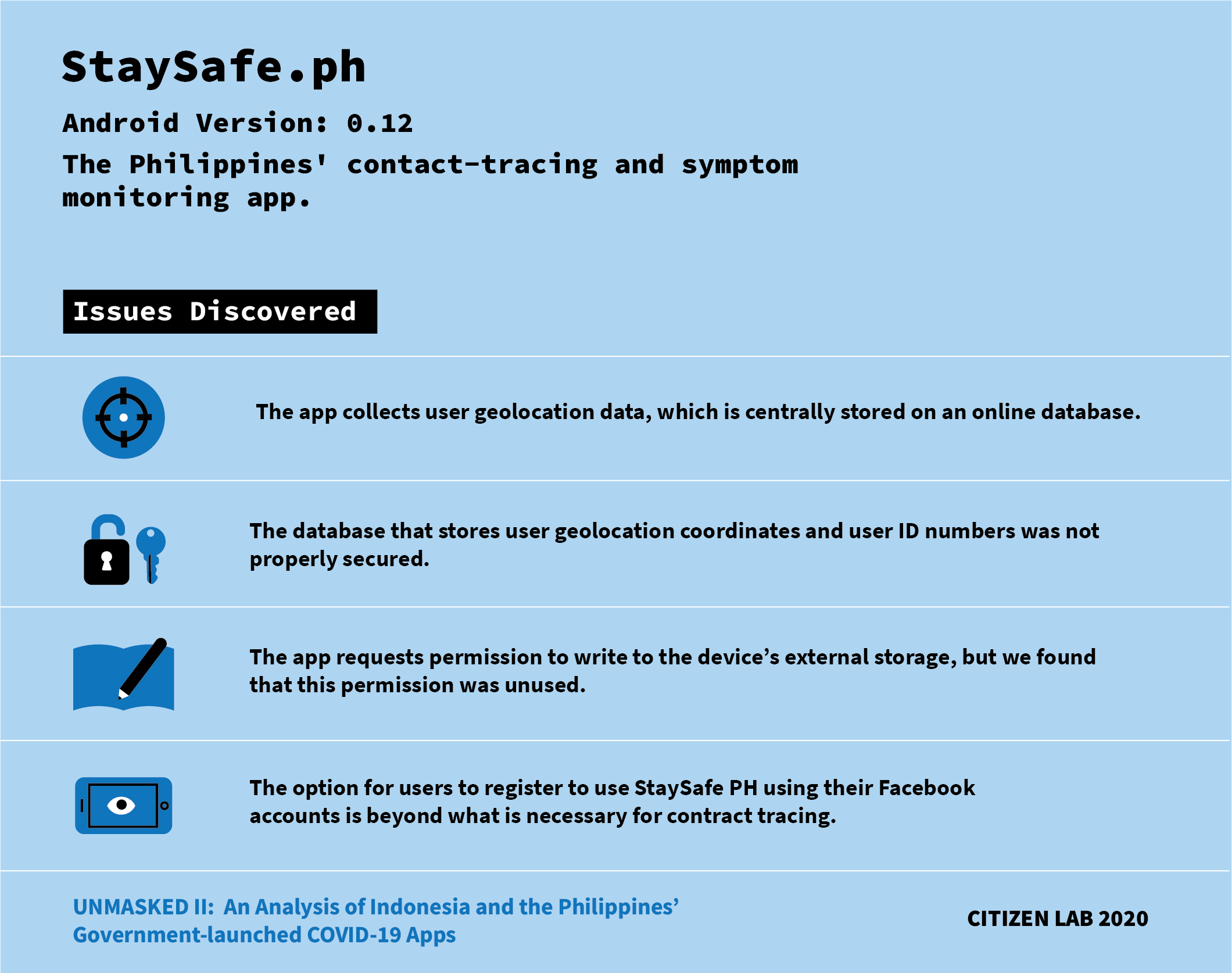
We discovered the following issues with the StaySafe PH app:
- The app collects user geolocation data, which is centrally stored on an online database. This central storing of user data is not necessary for digital contact tracing, and it presents privacy risks as it makes sensitive location and health data available to government actors and subject to disclosure in data breaches.
- The database that stores user geolocation coordinates and user ID numbers (referred to as universally unique identifiers, or UUIDs) was not properly secured. Full contents of this database could be accessed using specially crafted requests using the credentials of ordinary accounts. We believe that real-world identity could be inferred using this leaked information. For example, if an attacker knew the victim’s home and work location, they could find the victim’s UUID by searching for the victim’s changing geolocation from the geolocation coordinates of all users. Once the victim’s UUID is determined, their health status and whereabouts can be easily tracked using another public API.
- The app requests permission to write to the device’s external storage, but we found that this permission was unused.
- The option for users to register to use StaySafe PH using their Facebook accounts gives StaySafe PH access to identifiable information that is beyond what is necessary for contact tracing. If the user chooses to log in with Facebook, StaySafe PH’s developer would receive information from the user’s Facebook account such as the Facebook account’s unique ID, first and last name, profile picture, and email address. Logging on to the app using a Facebook account allows the StaySafe PH developer to associate information collected within the app (e.g., location and COVID-19 status) with the user’s online identity (e.g., Facebook account and email address), forming a more complete understanding of an individual’s life.
How did StaySafe’s developers address the security vulnerability?
Multisys, StaySafe PH’s developer, addressed our vulnerability disclosure by first publishing an update to the app. We had found this app update to be insufficient, because we were still able to access the unsecured database using the technique discovered from using the older version of the app. After we notified them of this problem, they restricted access to the database.
What is the COVID-KAYA app used for? And what issues did you discover?
The COVID-KAYA app is designed for local government units (or barangays), hospitals, and laboratories to submit and view COVID-19 cases, contacts, and patient information. The app is intended to be used by health workers and administrators and not the general public.
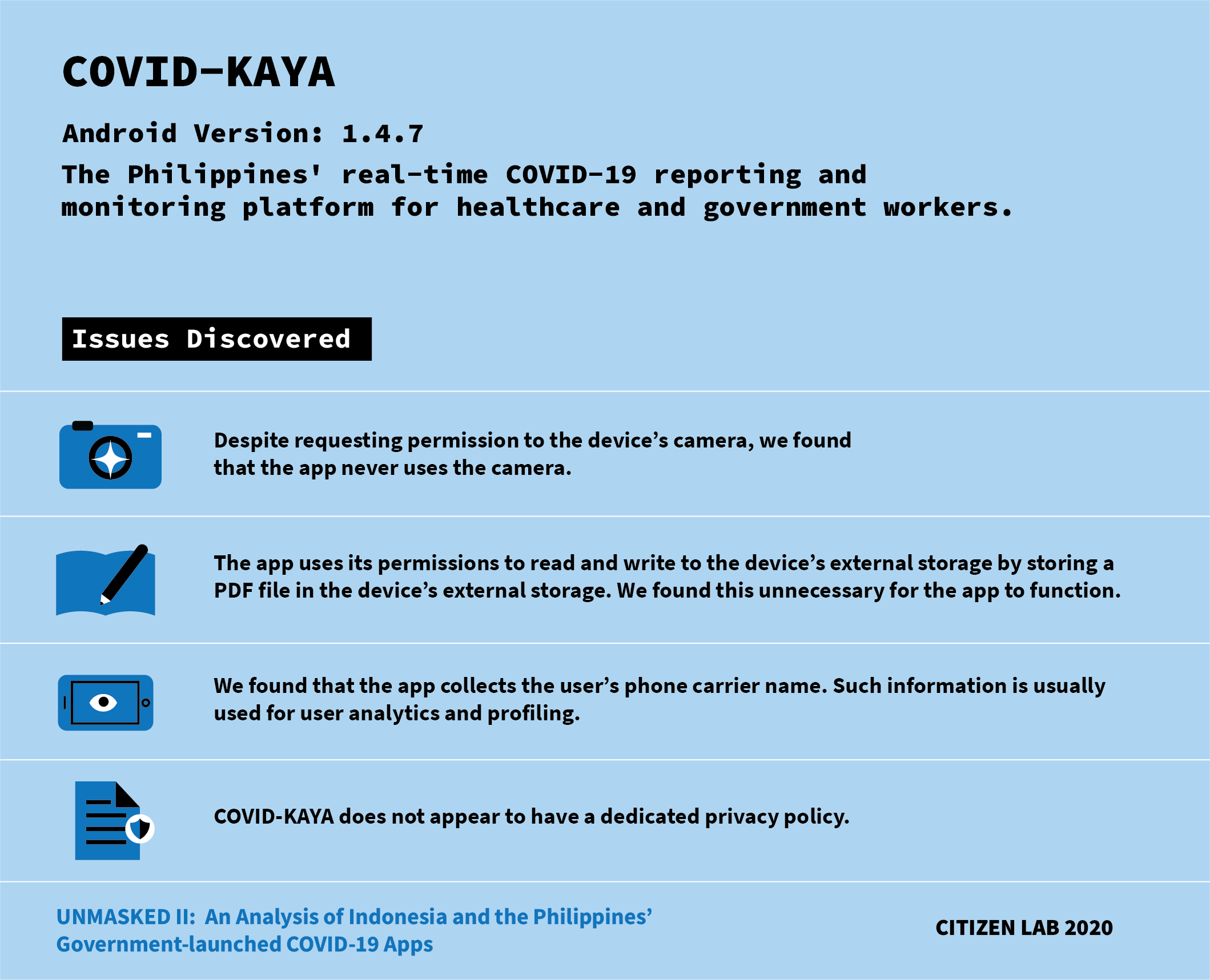
We discovered the following issues with the COVID-KAYA app:
- Despite requesting permission to the device’s camera, we found that the app never uses the camera.
- The app uses its permissions to read and write to the device’s external storage by storing a PDF file in the device’s external storage. We found this unnecessary for the app to function.
- We found that the app collects the user’s phone carrier name. Such information is usually used for user analytics and profiling.
- COVID-KAYA does not appear to have a dedicated privacy policy. Instead, its Google Play store page lists a link to a privacy policy which brings you to The World Health Organization’s Privacy Policy. However, the WHO’s Privacy Policy only pertains to WHO websites (“all sites within the ‘who.int’ domain name”), and thus it cannot be applied to the COVID-KAYA app.
How do the findings of COVID-KAYA relate to the issues previously reported?
We previously reported on two security vulnerabilities within the COVID-KAYA app.
The first vulnerability that we identified was an unprotected API used internally within the app that returned a complete list of the app’s registered users, including their full names and other personal information.
The second vulnerability we discovered was that the app’s administrator credentials can be found in the program code. An attacker who finds these credentials can log into the administrative dashboard and retrieve the list of the app’s registered users, including their full names.
These two vulnerabilities were discovered in our process of analyzing the app to understand how it used its permissions. The two vulnerabilities indicate the developer’s oversight in protecting collected user data. The more permissions that were used, the more data an app collects. Yet the more data an app collects, the more it can leak when vulnerabilities are found, therefore causing more harm to the users.
What is the difference between a permission and a dangerous permission?
Permissions allow apps to interact with a device’s hardware or perform certain functions, such as being able to view information about WiFi networks nearby. Google categorizes dangerous permissions as permissions that “could potentially affect the user’s privacy or the device’s normal operation,” such as access to a device’s photos, camera, location, contacts, calendar, phone status, and other access to sensitive user information. Dangerous permissions are not necessarily harmful, but due to the sensitivity of the information that they can be used to collect, their use can give rise to or magnify the impact of vulnerabilities.
What is the difference between dangerous permissions and vulnerabilities?
A vulnerability is a weakness in a system that can be exploited by a threat source. Dangerous permissions, while not necessarily harmful, can give rise to vulnerabilities, as seen in the case of StaySafe PH. StaySafe PH collected user location data through their app, requiring it to obtain a dangerous permission, namely the permission to acquire the device’s precise location. We discovered a vulnerability in the authorization logic of the database which Stay Safe PH used to store users’ location data, which allowed an attacker to download the location data of all of the app’s users. This vulnerability was made possible in part due to its use of the dangerous permission. If StaySafe PH, like many other contact tracing apps, had not collected users’ location data, then their app would have been precluded from having this vulnerability in the first place.
What are unused permissions?
An unused permission is a permission that an app has declared that it may request, but never requests, or that it requests, but never uses. For instance, an app may request permission to access the camera, but never actually use the camera to take a photo or a video. In such a case, the camera permission is unused. Although unused permissions themselves do not pose serious security and privacy risks, they do present a threat if the app is compromised by an attacker, as an attacker with the capability of remotely executing code in the app would additionally acquire the unused permissions.
What can app developers do to better protect the users of public health apps?
One thing app developers can do is to follow the principle of “data minimization,” whereby the app or tool “should collect the least possible information” that is necessary for achieving its objective. Collecting only highly relevant information can help mitigate the security risks that result from high-volume big data collection.
App developers can also refer to ethical guidelines for COVID-19 apps drafted by the following organizations/institutions:
- World Health Organization
- Electronic Frontier Foundation (EFF)
- Amnesty International
- Oxford Internet Institute