We confirm that two members of Serbian civil society were targeted with spyware earlier this year. Both have publicly criticized the Serbian government. We are not naming the individuals at this time by their request. The Citizen Lab’s technical analysis of forensic artifacts was conducted in support of an investigation led by Access Now in collaboration with the SHARE Foundation. Researchers from Amnesty International independently analyzed the cases and their conclusions match our findings.
In an investigative collaboration with Access Now, the Citizen Lab has analyzed forensic artifacts from the iPhone of award-winning exiled Russian investigative journalist Galina Timchenko and found with high confidence that on or around February 10th, 2023 it was infected with NSO Group’s Pegasus spyware.
Citizen Lab found an actively exploited zero-click vulnerability being used to deliver NSO Group’s Pegasus mercenary spyware while checking the device of an individual employed by a Washington DC-based civil society organization with international offices. We refer to the exploit chain as BLASTPASS. The exploit chain was capable of compromising iPhones running the latest version of iOS (16.6) without any interaction from the victim.
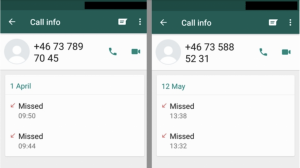
The May 2019 WhatsApp Incident As reported in May 2019, WhatsApp identified and shortly thereafter fixed a vulnerability that allowed attackers to inject commercial spyware on to phones simply by ringing the number of a target’s device. Today Oct 29th, WhatsApp is publicly attributing the attack to NSO Group, an Israeli spyware developer that also […]
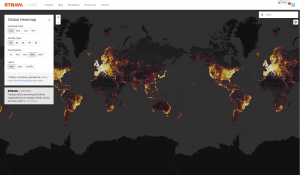
The post covers several categories of information that can be gleaned from examining Strava’s fitness tracker data, ranging from enabling the identification of secret military facilities in “dark areas” to specific identifiable behaviour patterns of at-risk individuals.
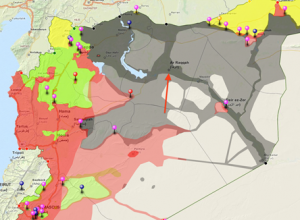
Citizen Lab Research Fellow John Scott-Railton is one of the authors of a report entitled “Behind the Syrian Conflict’s Digital Frontlines,” released today by FireEye, that documents a hacking operation that successfully breached the Syrian opposition.
This report describes a malware attack on a Syrian citizen media group critical of Islamic State of Iraq and Syria (ISIS). Though we are unable to conclusively attribute the attack to ISIS or its supporters, a link to ISIS is plausible. The malware used in the attack differs substantially from campaigns linked to the Syrian regime, and the attack is against a group that is an active target of ISIS forces. In the interest of highlighting a developing threat, this post analyzes the attack and provides a list of Indicators of Compromise.