Research
In April 2010, China Telecom’s network announced incorrect paths to 50,000 IP prefixes, referred to as a “hijack”. The politically sensitive nature of some of the IP prefixes that were hijacked brought this incident to the attention of the US government. It raises many important questions about how we characterize and reason about large-scale routing incidents when they occur.
Citizen Lab Director Ron Deibert has published a new article titled “The Growing Dark Side of Cyberspace ( . . . and What To Do About It)” in the Penn State Journal of Law & International Affairs, Volume 1, Issue 2, November 2012.
Google Policy Fellow Kieran Bergmann published an article for the Asia Pacific Memo. Bergmann’s article looked at Thailand’s lese majeste cases and the government’s method of controlling cyberspace.
Citizen Lab and Canada Centre for Global Security Studies Visiting Research Fellow in International Broadcasting Karl Kathuria wrote an article discussing the issues facing broadcasters online.
This is an update to our November 2011 report titledThe Canadian Connection: An investigation of Syrian government and Hezbullah web hosting in Canada, which examined the use of web servers based in Canada, the U.S., and European countries to host Syrian government websites and websites of the Lebanese political party Hezbullah. Our findings indicate that, while many of the websites we examined in 2011 have changed hosting providers, a number of Syrian government and Hezbullah websites still maintain an online presence through the services of North American and European web hosts.
Ethiopia remains a dangerous country in which to express dissent online. The recent conviction of a number of bloggers and journalists, combined with the country’s history of filtering critical political content online, demonstrates the restrictive nature of the country’s information environment. This blog post describes recent developments in the country and reports on the results of ONI testing conducted in September 2012.
In this report, Citizen Lab Security Researcher Morgan Marquis-Boire describes analysis performed on malicious software used to compromise a high profile dissident residing in the United Arab Emirates. The findings indicate that the software is a commercial surveillance backdoor distributed by an Italian company known as Hacking Team. The report also describes the potential involvement of vulnerabilities sold by the French company, VUPEN.
In this technical brief, Citizen Lab Senior Security Analyst Seth Hardy presents a detailed analysis of IEXPL0RE RAT, a remote access trojan targeting human rights-related organizations.
2012 Google Policy Fellow Kieran Bergmann wrote an article titled Outsourcing Censorship for the Canadian International Council on how governments in Asia are increasing their efforts to control online content.
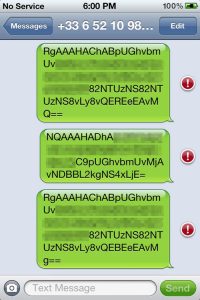
This report, written and coordinated by Citizen Lab Technical Advisor Morgan Marquis-Boire, analyzes several samples we believe to be mobile variants of the FinFisher Spy Kit targeting iPhone, Android, Blackberry, Windows Mobile and Symbian platforms. It is a follow-on to a previous research brief, From Bahrain with Love: FinFisher's Spy Kit Exposed?, that analyzed several pieces of malware targeting Bahraini dissidents.