NSO Group
Citizen Lab senior researcher John Scott-Railton discusses why WhatsApp is suing NSO Group after discovering their spyware was used to target 1,400 users—100 of whom were members of civil society—and why this is a significant bellwether.
As part of our investigation into the incident, Citizen Lab has identified over 100 cases of abusive targeting of human rights defenders and journalists in at least 20 countries across the globe, ranging from Africa, Asia, Europe, the Middle East, and North America that took place after Novalpina Capital acquired NSO Group and began an ongoing public relations campaign to promote the narrative that the new ownership would curb abuses.
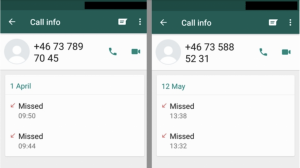
The May 2019 WhatsApp Incident As reported in May 2019, WhatsApp identified and shortly thereafter fixed a vulnerability that allowed attackers to inject commercial spyware on to phones simply by ringing the number of a target’s device. Today Oct 29th, WhatsApp is publicly attributing the attack to NSO Group, an Israeli spyware developer that also […]
We urge you to seriously engage with the significant issues raised by your Authority’s investment with Novalpina Capital and we look forward to your outstanding reply to our correspondence dated May 24, 2019.
18 June 2019 Dear Yana and Stephen Peel, We write to you in light of recent reporting indicating that you both own a stake in Novalpina Capital LLP. As Yana Peel has recently expressed that she believes criticism of NSO Group is “misinformed,” we thought it appropriate to specifically draw Ms. Peel’s attention to the […]
Given Novalpina Capital’s recent acquisition of NSO Group and the obvious human rights concerns raised by NSO Group’s business practices, Citizen Lab’s Ronald Deibert seeks a response from the South Yorkshire Pensions Authority regarding how its investment in Novalpina is consistent with the Authority’s Policy and what measures were taken by the Authority to inform and educate pension fund contributors and members regarding NSO Group.
A recently discovered security vulnerability on WhatsApp, currently used by over 1.5 billion people worldwide, has been found to have been exploited by NSO Group developed spyware.
Spyware developer NSO Group is usually quick to dismiss the evidence that its customers have abused its Pegasus mobile phone spyware. This pattern of denials was repeated in a recent 60 Minutes investigation, which gives a rare look into NSO Group’s management.
The window of a murdered Mexican journalist was targeted with Pegasus, a spyware product which can secretly access the contents of a phone and turn on its camera and microphone.
This research brief details how Griselda Triana, journalist and the wife of slain journalist Javier Valdez Cárdenas, was targeted with NSO Group’s Pegasus spyware in the days after his killing.