Who’s Watching Little Brother? A Checklist for Accountability in the Industry Behind Government Hacking
We are releasing a more comprehensive “checklist” consolidating our thoughts on how best to confront the lack of accountability in the commercial spyware trade.
Over the past few years, Citizen Lab research has delved into the growing market for advanced commercial spyware and the use of such spyware to target and compromise civil society actors. We have released numerous reports documenting the deployment of tools such as FinFisher, Hacking Team’s Remote Control System (RCS), and NSO Group’s Pegasus against peaceful advocates, journalists, and others who were deemed political threats by government agencies. We have looked at dual-use technology more broadly as well and commented on policy options for addressing the serious human rights repercussions of this market.
Today, we are releasing a more comprehensive “checklist” consolidating our thoughts on how best to confront the lack of accountability in the commercial spyware trade. What follows below is a short excerpt from the article.
Where some see insecurity, others see a welcome market opportunity. Indeed, business is booming for a specialized market to facilitate the digital attacks, monitoring, and intelligence-cum-evidence-gathering conducted by government entities or their proxies. Private companies with the advanced technical expertise and real passion for digital compromise assist governments in staying on the cutting edge of scientific and technological developments and deploying the latest digital attack techniques. (Encryption? Circumvention? Anonymity? No problem.) Most of us have no idea who these companies are, how they vet their clients, whether they have any knowledge of human rights issues, or whether they answer to anyone other than their CEOs or shareholders.
Sure, some of these companies have come to light, following challenging research and reporting on their products and services. Hacking Team. Gamma Group / FinFisher. NSO Group. An accumulating body of evidence over the last several years has shown how the vendors of commercial spyware are not averse to selling their wares to some of the world’s most notorious autocratic regimes. Private companies have equipped regimes known to lack rule of law, abuse human rights, or engage in violent internal conflict, enhancing the ability of such regimes to further weaken and punish their citizenry and opposition. Spyware manufactured by Italy’s Hacking Team and the UK/Germany-based Gamma Group, for example, was determined to be the weapon of choice for a dubious group of countries, including the United Arab Emirates, Morocco, Sudan, and Ethiopia. In one particularly egregious example, Ahmed Mansoor, an activist in the UAE, was targeted over the course of five years with multiple forms of advanced commercial spyware, including that offered by Gamma Group, Hacking Team, and NSO Group. The NSO Group spyware even incorporated three distinct zero-day exploits capable of compromising the operating system of any iPhone; such zero-day exploits are reported to sell for as much as a million dollars.
Far from using this spyware solely to track what might be considered legitimate targets, these countries and their shadowy agencies have repeatedly used them to get inside the computers of human rights activists, journalists, opposition politicians, and even health advocates supporting a soda tax in Mexico. Some of the victims of these campaigns have found themselves arrested and tortured. Leaked emails from certain companies reveal that, despite public assurances by executives, the vendors seem cavalier about these type of abuses, have few internal checks in place to prevent them, and, indeed, knowingly court the clandestine agencies responsible for such abuses. Despite these alarming incidents, however, the dynamics of and participants in the market at large remain opaque.
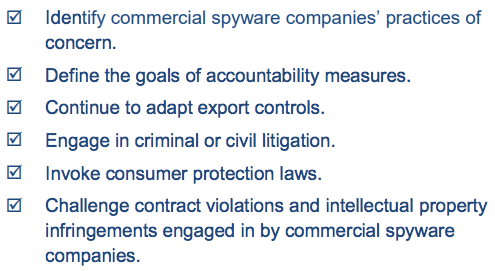
We recommend pursuing the following “constellation of practices” to address the lack of accountability in the market for commercial spyware:
| ☑ | Identify commercial spyware companies’ practices of concern. |
| ☑ | Define the goals of accountability measures. |
| ☑ | Continue to adapt export controls. |
| ☑ | Engage in criminal or civil litigation. |
| ☑ | Invoke consumer protection laws. |
| ☑ | Challenge contract violations and intellectual property infringements engaged in by commercial spyware companies. |
| ☑ | Develop an accountability framework specific to the private market for digital surveillance. |
| ☑ | Explore industry self-regulation. |
| ☑ | Build out communities of practice to raise public awareness and document abuses. |
Read the full article (PDF)