Annotated Bibliography
Dual-Use Technologies
This document provides a high-level introduction to deep packet inspection, Internet filtering, and targeted intrusion dual-use technologies with the aim of familizaring the reader with their key technical features, the surrounding international human rights law framework, and some of the leading research to date on their deployment.
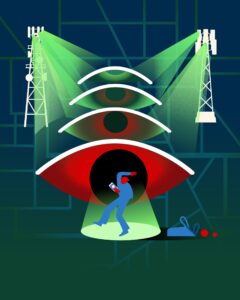
As cybersecurity issues have mounted, dual-use technologies have proliferated. These technologies can be used for legitimate and socially beneficial purposes. However, they can also undermine human rights depending on how they are deployed. For example, network traffic management technology such as deep packet inspection (DPI) and Internet filtering tools can be used legitimately for traffic management. However, they can also be used to undermine human rights by blocking political content or intercepting communications. Malicious software built for “lawful interception,” such as zero-day exploits, can lead to human rights abuses if there are improper safeguards or oversight mechanisms in place.
The proliferation of these dual-use technologies stems in part from an increase in private companies who create suites of technology that are ready to be deployed by law enforcement and security agencies, allowing any government to access capabilities that were previously difficult to obtain. This growing appetite for cybersecurity products and services has created a large and growing industry with proven abuse potential.
To help better understand how these technologies function, particularly in the context of human rights defenders and civil society organizations, Citizen Lab researchers have assembled an annotated bibliography. This document provides a high-level introduction to deep packet inspection, Internet filtering, and targeted intrusion dual-use technologies with the aim of familizaring the reader with their key technical features, the surrounding international human rights law framework, and some of the leading research to date on their deployment. The annotated bibliography also contains a glossary of defined technical terms that should help familiarize the reader with common language in this domain.