It’s time to dissect the questionable practices and foreseeable misuse at the heart of the spyware trade
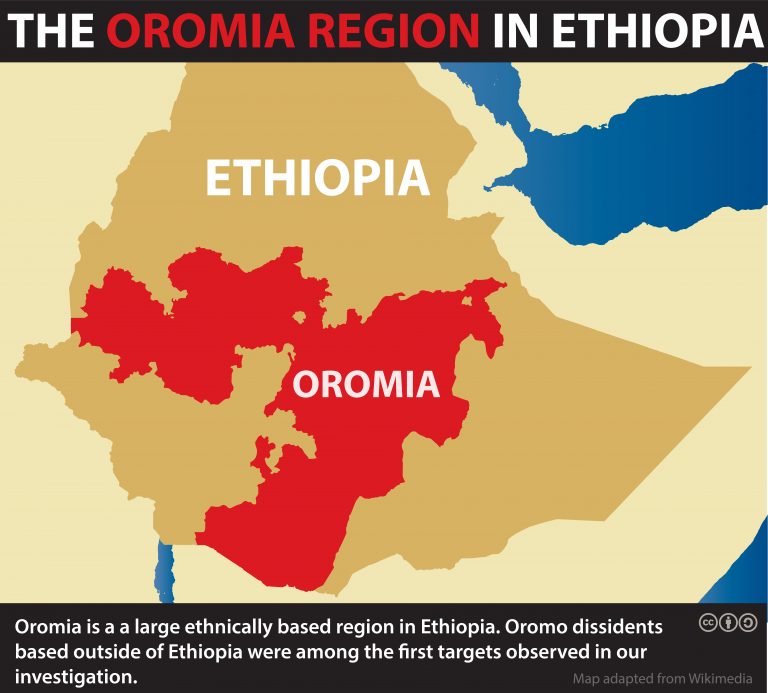
Citizen Lab’s publication today of the “Champing at the Cyberbit” report marks at least the fifth release since 2013 of evidence linking the Ethiopian government to misuse of spyware against civil society actors. As with prior reports, targets we discovered are based in Canada, the United States, Europe, and elsewhere around the world, demonstrating expansive extraterritorial surveillance made possible for the Ethiopian government by commercial spyware. New to this report: the list of spyware used has grown to include not just Hacking Team’s RCS and Gamma Group’s FinSpy, but also “PC Surveillance System” (PSS), a product offered by Cyberbit (a subsidiary of Elbit Systems, based in Israel). The targets also include our very own US-based research fellow, Bill Marczak.
Our research, which documents new attacks against civil society by government actors based in and operating from Ethiopia, highlights the need for clear legal pathways for extraterritorially-targeted individuals to seek recourse. At this juncture, the Ethiopian government’s penchant for commercial spyware is notorious, as is its pattern of digital espionage against journalists, activists, and other entities—many of which are based overseas—that seek to promote government accountability and are therefore viewed as political threats. Yet the Ethiopian government and others like it have faced little pressure to cease this particular strain of digital targeting.
A case in point: In 2014, supported by the Electronic Frontier Foundation, an American citizen who was born in Ethiopia filed a lawsuit against the Ethiopian government in federal court after research revealed that his computer was infected with FinSpy spyware. The plaintiff, using the pseudonym Kidane, alleged that the Ethiopian government had violated the US Wiretap Act (as well as state law regarding intrusion upon seclusion) when it used FinSpy to infect his computer and engage in ongoing interception, monitoring, and collection of his communications and other data. The court dismissed the case in May 2016, concluding that “the Wiretap Act does not create a private cause of action against a foreign state and that the plaintiff’s state-law tort claim is barred by the Foreign Sovereign Immunities Act (FSIA).” While the plaintiff appealed, the U.S. Court of Appeals for the District of Columbia Circuit affirmed the dismissal in March 2017, and a subsequent petition for rehearing en banc was denied.
The grounds upon which the Kidane dismissal was affirmed establish a troubling precedent. With respect to an inquiry of whether the tort in question occurred entirely in the United States, as required to proceed against a sovereign under the non-commercial tort exception of the FSIA, a digital tort is considered to occur where (a) the intent is formed to commit the tort; (b) the acts of computer programming required to commit the tort are undertaken; and (c) the device is actually infected. Thus, even though a foreign government may infect devices and inflict significant harm within the United States on American citizens using digital tools, according to the court’s reasoning, digital compromise occurring within the United States is not enough. If any intent is formed or any programming occurs abroad, legal remedy is unavailable. Under this ruling, “transnational cyberespionage” is effectively never within the scope of jurisdiction afforded by the FSIA. And as our report today demonstrates, the Ethiopian government appears only emboldened to continue its hacking of law-abiding American citizens, despite multiple reports and extensive media coverage of these activities. Legislators may need to intervene to correct the dangerous precedent this ruling sets on the application of the FSIA to digital torts.
Of course, governments possess wider latitude than private citizens to challenge the digital espionage practices of other nation-states. Assuming that the targeting in this case was undertaken by Ethiopian government actors without U.S. government knowledge, such targeting contravenes norms surrounding state sovereignty, international law enforcement, and intelligence cooperation. Depending on the states involved, the use of spyware may even bypass established mutual legal assistance processes. Discovery of state spyware operations against private citizens that have not been previously cleared with counterparts in the relevant jurisdiction could serve as a basis for démarche. The use of spyware with the capabilities identified in this study may also violate criminal laws related to computer fraud and abuse, and those related to the interception of private communications without consent or prior lawful authorization, including in the United States. Indeed, the U.S. has previously issued indictments against state-linked actors in Russia, China, and Iran on charges of computer fraud and abuse (among others).
In seeking recourse for digital espionage, it is important to note that many governments do not act alone in pulling off these operations: they are actively supported by a thriving commercial spyware market. Commercial spyware companies have knowingly provided their products to “repeat offenders,” such as the Ethiopian government, as well as to other government entities with well-established track records of human rights abuses. It appears that in some instances, these sales had the approval of national export authorities, suggesting a stronger interest on the part of governments in equipping intelligence partners and growing their cybersecurity industry than in protecting human rights.
Commercial spyware companies have also incorporated in the design of their products certain techniques that involve spoofing legitimate companies—for example, by packaging their spyware alongside legitimate software such as Adobe Flash Player—in order to deceive a target, enhancing the likelihood of target infection and spyware persistence. The result is not only the infection of targeted individuals’ devices, but also the undermining of security of the wider digital ecosystem. Spyware companies have profited, while civil society and legitimate ICT businesses have borne the costs of foreseeable misuse of spyware products and services.
Today’s report examines the role of Cyberbit, an Israel-based subsidiary of Elbit Systems and the provider of PSS. While we do not know the level of scrutiny applied to Cyberbit’s sale of PSS to Ethiopian entities under Israeli export regulations, it is clear that Ethiopia has for years been known to misuse spyware against civil society actors in violation of their human rights. The fact that a sale must have taken place in spite of this reality raises a number of concerns regarding Cyberbit’s due diligence practices and any assessment of human rights impact undertaken during the export licensing process.
Moreover, there are indications that Cyberbit may be misappropriating the names and trademarks of legitimate individuals and/or companies–to masquerade as trusted software, or acquire so-called “code signing certificates,” which can manipulate targets or targeted computers into believing that their products are not malicious. The PSS spyware appears to prey in particular on a user’s trust in Adobe Systems and widespread reliance on Adobe Flash Player: we observed PSS bundled with real Adobe Flash Player software, and attempts to spoof legitimate Adobe resources through use of Adobe and Flash trademarks. Such practices may provide grounds for legal action or other remedies by those who are illegitimately targeted and/or falsely impersonated. As in the case of Finfisher—which impersonated Mozilla’s products, resulting in the company sending a cease and desist letter to FinFisher’s parent company, Gamma Group—Cyberbit’s use of fake Adobe Flash Player updates may likewise give rise to various intellectual property claims. At the very least they demonstrate that if left unchecked, spyware companies will resort to deceptive, unethical, and legally questionable practices.
In sum, our latest report adds yet more evidence to the long list of cases involving the abuse of powerful dual-use surveillance technologies. Yet again, we have uncovered a company’s products and services—ostensibly sold to assist in law enforcement and national security investigations—used by repressive governments to target critics of the regime instead. As more governments develop an appetite for these products and services, we expect to uncover more troubling cases such as these. Mitigating these issues will require a comprehensive review of legal, regulatory, and corporate social responsibility measures by governments and the international community.
Read the full letter to Cyberbit and their response
Read the full letter to Adobe and their response
Read the full letter to Citizen Lab from FlashPoint IP Ltd. regarding unauthorized use of its name and address in the spyware’s code-signing certificate

